Dictators target the power of the Internet
An ancient form of protest, self-immolation struck an even bigger impact in our technological age. The call for revolution spread across Twitter and Facebook at the speed of a runaway computer virus from North Africa to the Middle East and beyond.
By Joe Fitzgerald
The Guardsman
A man in Tunisia lit himself on fire, and a revolution was born.
An ancient form of protest, self-immolation struck an even bigger impact in our technological age. The call for revolution spread across Twitter and Facebook at the speed of a runaway computer virus from North Africa to the Middle East and beyond.
A few short weeks later, dictator Zine al-Abidine Ben Ali was toppled in Tunisia.
The Tunisian’s success ignited Egypt. Realizing he had a rebellion on his hands, President Hosni Mubarak moved quickly to hit the kill switch on Egypt’s cell phones and Internet.
The Internet itself was not the subject of the Egyptian’s revolt — the rising cost of food, lack of jobs for the educated and working class and severe corruption in their government is a short list of their many grievances. The Internet was a necessary tool in their cause.
After a short time, Mubarak bowed to international pressure and restored communications for the country, and through patience and peaceful protest the Egyptians succeeded in ousting the corrupt dictator.
Among the worst of Mubarak’s many missteps was the blatant censorship of his people. He made digital martyrs of all Egyptians and crystallized the world’s attention on his nation.
Complex censorship
China, ranked 168th by Reporters Without Borders in terms of press freedom, is a leading example of how to make censorship effective in the technological era.
If all China did was cut off their people’s access to the Internet completely, they wouldn’t succeed for long. The U.S. military actually has the technical means to reverse widespread Internet loss, according to a recent Wired report. But China employs much stealthier and surgical means of silencing its citizens.
Benevolently titling its practice the “Golden Shield Project,” the Chinese government blocks specific Internet sites and videos through major web portals like Google, YouTube, Yahoo, Facebook and Twitter. The government arrests citizens who become too loud or too revolutionary and imprisons and persecutes the journalists in China who want to expose these policies to the world.
Ironically, China even blocked Internet access to reports on the Tunisian and Egyptian uprisings themselves, according to a Council of Foreign Relations report. This combination of technical savvy and atmosphere of fear is impossible for any one military weapon to overcome.
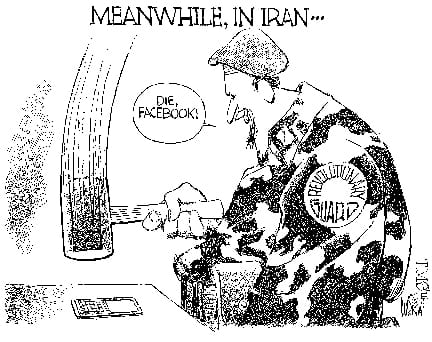
Iran and china
Iran, under President Ahmadinejad and Supreme Leader Ayatollah Khamenei, spreads anti-U.S. and anti-reform propaganda on a near daily basis. Almost all of their tactics are ripped from China’s playbook.
Like China, Iran has been censoring its people and journalists through imprisonment and intimidation for years. A powder keg of oppression, governmental abuse of power and a strong economic downturn have long been pushing Iranians to their limits.
It should come as no surprise, then, that the downfall of Ben Ali and Mubarak have emboldened them — uprisings and mass unrest have reignited in Iran.
join the fight
The U.S. and other countries in the world have many technical and military means to combat censorship in Iran.
The U.S. government itself has aircraft that can temporarily restore Internet use to entire countries. Diplomatic pressure can also give an oppressive regime a final push out the door. As citizens, we can contribute as well. Proxy Internet servers in the U.S. can be used to allow Iranian citizens to access sites blocked by the government. Additionally, “ghost” Twitter accounts that claim to be in Iran, but in reality are elsewhere in the world, can be setup to overload government censors.
We shouldn’t abandon the Iranians in their fight or send them hollow words. As allies to all people fighting for freedom, the international community needs to empower their nation with one of the most formidable weapons of any era — the freedom of speech.